How does the BSI certification of the technical security system (TSS) work?
What is a protection profile?
The BSI (Federal Office for Information Security) specifies in protection profiles which technical requirements must be met in order to achieve the objective of the KassenSichV. The security profiles describe security objectives and requirements according to the security functions of the components. However, the product-specific specification is made by the manufacturer.
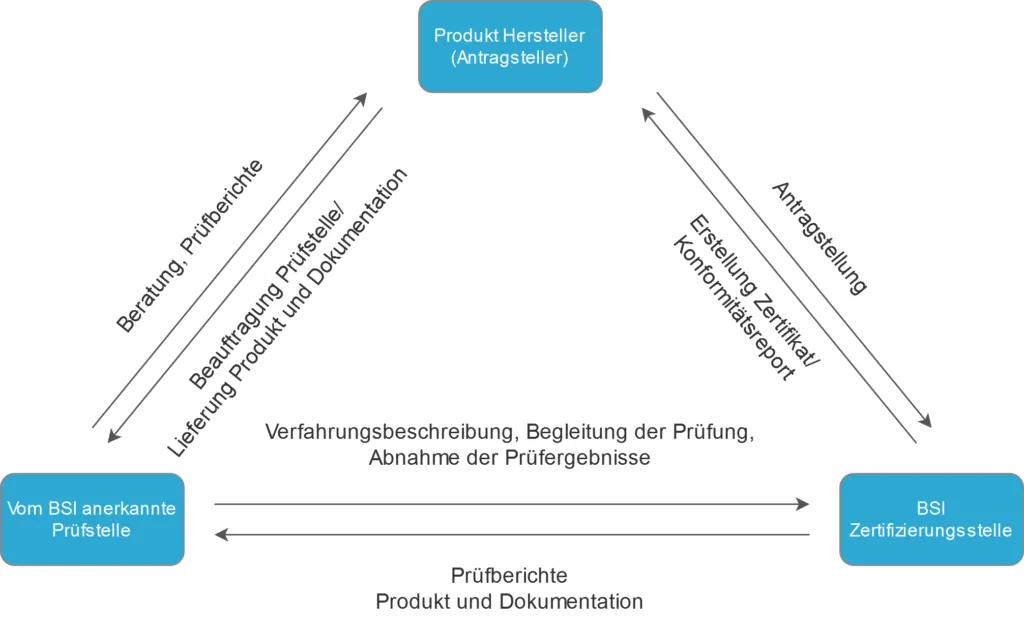
How is the certification of the technical security system (TSS) carried out?
The CSP-L and the SMAERS components are certified independently of each other. In the process, the compliance of the components with the protection profiles is checked by an evaluator (a company accredited by the BSI). The evaluation report is then forwarded to the BSI for review.
With a positive conclusion, the components each receive a certificate. Finally, the components in the network (= technical security system) are tested by the TR test. If the TSS is correct and implemented according to the applicable requirements, it is certified.
When evaluating the SMAERS component, there are strong synergies with the TR test, i.e. the TR test can only be passed positively if the SMAERS component has also been positively evaluated. Therefore, after receiving the SMAERS certificate, the final TSS certification can be expected soon. The BSI issues the certification, which must be renewed every five years.
